Easyofdeanon.fig [BEST]
: Mapping partial names or addresses to potential real-world identities.
: Automating the process of scraping social media, public records, and leaked databases to find "linkable" traits. easyofdeanon.fig
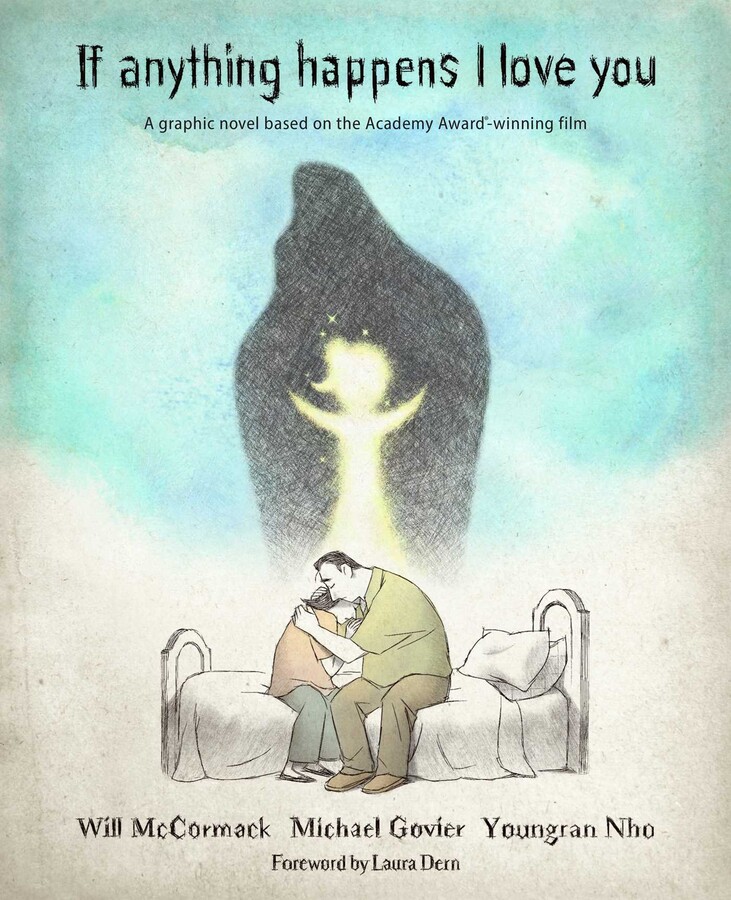
The use of de-anonymization tools like those defined by an easyofdeanon.fig file is controversial. While researchers use them to , the same tools can be used for "doxing" (revealing private information with malicious intent). Most ethical guidelines for OSINT emphasize using these tools only on datasets where you have explicit permission or for defensive security auditing. : Mapping partial names or addresses to potential
: The "easy" prefix suggests a pre-configured or "turn-key" setup designed to lower the barrier for researchers to run complex de-anonymization scripts without manual coding. Technical Context: Files and Frameworks While researchers use them to , the same
: Security practitioners use these files within terminal environments to quickly call de-anonymization commands like deanon -t targets.fig . Ethical and Legal Considerations