Experience world-class virtual golf with Golfzon Vision WAVE,
offering realistic 3D courses and global competition on any device.
*Compatible with both WAVE and WAVE Play
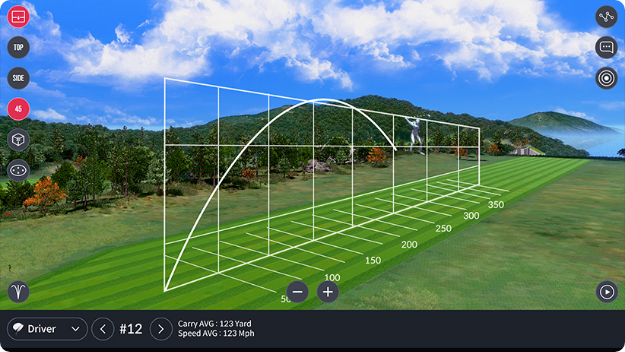
WAVE Skills is a mobile app that displays
detailed shot
data and swing analysis for
Golfzon WAVE users,
enabling
performance
tracking and improvement.
*Exclusive to WAVE
: If you want to test the software


WAVE Watch app connects to
your WAVE
device via Bluetooth for instant shot results
on your smartwatch, enhancing your golf
experience.
*Compatible with
Apple Watch and Galaxy Watch 4,5
If you have already purchased a license and


Vision WAVE's mobile version is
set to launch in Q4 2023, offering support for both
iOS and Android devices.
*Compatible with
both WAVE and WAVE Play
Downloading or using "cracked" versions of security software


WAVE Arcade is a mobile app that offers
6 innovative arcade games
instead of
traditional 18-hole play.
*Compatible with
both WAVE and WAVE Play
: If you want to test the software legally, ESET offers a 30-day free business trial with no credit card required. Risks of "Cracks" and Unofficial Keys
: This version was officially released in June 2022 and introduced features like a minimal installer for deployment and a complete revision of the email client protection module.
: Counterfeit versions rarely receive the critical security signatures needed to protect against new threats.
If you have already purchased a license and lost your information, you can use the ESET Lost License tool to have your credentials resent to your registered email. Download ESET Endpoint Security for macOS
: ESET now uses the ESET PROTECT Hub to manage licenses via account credentials, eliminating the need to manually track activation keys.
: "Cracked" software often requires you to disable your antivirus during installation, allowing malicious code to infect your system.
Downloading or using "cracked" versions of security software like is strongly discouraged. These files are frequently used as delivery vehicles for malware, ransomware, and credential stealers, which can compromise the very systems you are trying to protect.