4Front ProAudio VST/VSTi

| 4FRONT TruePianos TruePianos is a new virtual piano VSTi based on a combination of physical modeling, synthesis and sampler techniques. Using a combination of the best what these individual technologies have to offer, TruePianos provides great playability by allowing itself to be easily adjusted to the combination of your unique playing style and the specific characteristics of your MIDI keyboard, instead of the other way around. It doesn't attempt to meticulously simulate existing pianos but instead provides realistic and expressive range of piano modules, each with individual dry sounding presets that you 'just play'. |
||
Stormatt.exe Apr 2026StormATT.exe is a reminder that cyber warfare is an arms race of adaptability. For defenders, the goal isn't just to block the file, but to understand the —from initial access to the final objective. Are you analyzing this for or looking for specific YARA rules to detect it in your environment? StormATT.exe The primary strength of StormATT is its modularity. Rather than carrying a massive payload that is easily flagged by antivirus (AV) signatures, the core executable often acts as a "loader." Once it gains a foothold, it calls back to a Command and Control (C2) server to download specific modules tailored to the environment—be it credential harvesting, lateral movement, or data exfiltration. 2. Stealth and Evasion StormATT In the modern threat landscape, the "one-size-fits-all" virus is a relic. Modern campaigns now rely on modular executables like . These are designed not just to infect a system, but to act as a versatile "Swiss Army Knife" for post-compromise activities. 1. Tactical Flexibility The primary strength of StormATT is its modularity For security teams, the presence of an executable like StormATT.exe is a high-severity alert. Defense requires a shift from "signature-based" detection to . Assuming the perimeter is already breached and verifying every request. |
||
| 4FRONT BASS MODULE (VSTi) The bass module is a morph between sample playback and a synthesizer. Original string excitation is sampled, and then sound is modeled. Playing chords will add extra fat rumble, like when playing a real bass guitar. Bass guitar range was artifically extended up and down, so that higher notes and parts can be played as well. |
||
|
4FRONT RHODE MODULE (VSTi)
A vintage Rhodes/Wurly typed piano module with gentle overdrive. This module reproduces the classic sound similar to Rhodes/Wurlitzer pianos. Module is not sample based, and the sound is generated on-the-fly, therefore there are no sampling layer switches - vintage rhodes overdrive is smooth, clean and continuous. Difference between Basic (free) and Pro (commercial) modules To get a common idea of what exactly is different, check the screenshots below: Basic version:
As you can see, basic version is generally lacking envelope, sensitivity/drive and room controls, that Pro version has. If you like to get this kind of controlling over 4Front Rhode sound, you may want to get Pro version. MP3 Demos |
||
| 4FRONT E-PIANO MODULE (VSTi) E-Piano module with a rich, warm and silky sound. It is quite unique by its character. The module is made with a hybrid technology, which involves sample playback and synthesizing within one case. For its quality, module has reasonable small size. |
||
|
4Front XLimiter (VST/DX)
A gentle and soft brickwall limiter processor. Primary design goals: - Master track brickwall compression - Vocal track compression - Solo track compression A special multistage algorithm provides a very soft transition envelope, thus rapid level changes at extreme Threshold level will not pump or distort as much as with the other processors. The limiter employs best properties of a single band processor, whereas additional techniques are used to provide advantages of "continuous multiband" processing. Usage: With the default settings it will limit the signal at 0dB. This is useful to plug into the master effect bin of a multitrack software. You can lower Threshold value to bring up the volume of the track. If you are limiting a vocal track - you can also set appropriate ceiling value to control the output volume. If you have deessing or disturbing frequencies problem, try using this effect as a vocal or solo processor. In most cases you will not need an additional de-essing, as XLimiter will handle those transients properly. 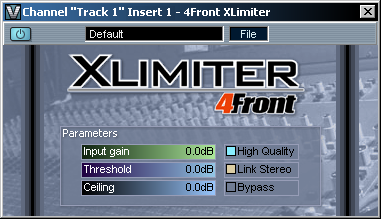 |
||
|
4FRONT AUXITER (VST/DX)
This is a high frequency refresher exciter-type plugin. It brings clarity to the high end by regenerating high frequency harmonics. Primary design goals: - Vocal enhancer - Per/track enhancer - Master track restoration/refreshment - Old tracks restoration Usage: First try to figure right Frequency slider value for your track, then control the Harmonic, Drive and Mix levels to get the best enhancement. 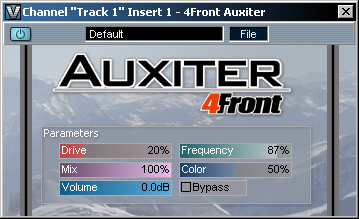 |
||
| 4FRONT SAND BRUSH (VST/DX) The plugin completely regenerates high frequencies, basing on the existing partials. The plugin can be used to apply on hihats and other percussive sounds with high frequency content, and also can be used on other tracks to add "sand". Depending on the settings, plugin can be also used to emulate the vintage vinyl sound. Primary design goals: - Sand for vocal and solo tracks - Bring life back to sampled strings - Track restoration (including MP3) - Vintage effect (to create vintage sound) The plugin contains multiple presets for various track types. 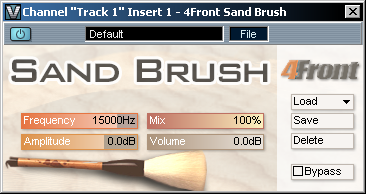 |
||
| 4FRONT CONTOUR MAX (VST/DX) The plugin is designed to change the basic frequency contour of a sound track, or the overall frequency balance of a master. Primary design goals: - Master processing - Per-track processing for balancing low and high end - Track restoration The plugin contains multiple presets for various track types. 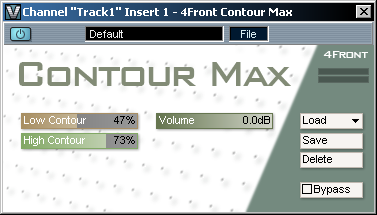 |